

A single undetected defect can bring an entire enterprise system to a halt, leading to missed deadlines, failed deployments, security breaches, and frustrated users, which are not just technical issues. They translate directly into revenue loss and reputational damage, yet many organizations still treat software testing as a final checkpoint instead of a continuous business safeguard.
As enterprises accelerate digital transformation, software systems are becoming more complex, interconnected, and release driven. While users expect flawless performance, today’s applications function within interconnected ecosystems that include cloud platforms, external APIs, mobile devices, and legacy infrastructure.
In highly connected systems like these, a minor breakdown can trigger broader consequences across the organization, including:
- Disruptions to core business operations
- Increased compliance and regulatory risks
- Loss of customer trust and brand credibility
Quality assurance is not limited to identifying defects before launch. When implemented correctly, QA testing enables enterprises to release faster without compromising stability or security.
For modern organizations adopting agile and DevOps practices, testing must evolve beyond manual checks and isolated test cycles. Enterprises need structured processes, the right mix of manual and automated testing, and testing strategies aligned with business goals.
This enterprise guide to software testing and quality assurance explores how organizations can build resilient, scalable, and high-quality software systems. It covers essential concepts, testing types, methodologies, tools, challenges, and best practices to help enterprises move from reactive testing to proactive quality management.
Quality Assurance vs Quality Control
Quality Assurance and Quality Control are both essential to delivering reliable enterprise software, but they address quality from different perspectives. Quality Assurance focuses on establishing the proper foundation for building software correctly, while Quality Control concentrates on verifying that the finished product meets expectations.
Quality Assurance is concerned with the processes used to develop software. It emphasizes defining standards, best practices, and workflows that guide teams throughout the development lifecycle.
Quality Assurance is embedded into the software lifecycle from the moment requirements are defined, carrying through design, development, and testing. Its primary objective is to reduce defects by guiding teams to follow clearly established processes. For large organizations, QA testing enables scalable operations, improves team coordination, and helps meet governance and compliance requirements.
Quality Control, by contrast, focuses on the software product itself. It involves testing and inspecting the application to identify defects once development is underway or complete. QC activities validate whether the software behaves as intended and meets functional, technical, and business requirements. This step is critical in enterprise systems where failures can impact multiple departments, customers, or integrations.
Rather than competing practices, QA and QC work best together. QA reduces the likelihood of defects by strengthening development practices, while QC ensures that remaining issues are detected before release. A balanced approach enables enterprises to deliver stable, secure, and high-quality software at scale.
In conclusion, Quality Assurance builds quality into the process to prevent defects, while Quality Control validates the final product to catch issues, together ensuring dependable and scalable enterprise software delivery.
| Aspect | Quality Assurance (QA) | Quality Control (QC) |
|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Benefits of Software Testing and Quality Assurance
Software Testing
-
Early Detection of Defects
Software testing enables teams to identify functional, performance, and security issues during the development lifecycle rather than after release. Early detection reduces the risk of failures in live environments and enables teams to resolve the problems before they affect customers or operations.
-
Better Software Reliability
Testing ensures applications perform consistently under real-world conditions such as high user traffic, heavy data loads, and complex system integrations. Software testing evaluates how systems behave across various scenarios, helping enterprises ensure stability and reliability in applications that support essential business processes.
-
Reduced Business and Operational Risk
By catching issues early, software testing minimizes the risk of downtime, system outages, and service disruptions. A proactive testing strategy supports uninterrupted business operations, lowers financial exposure, and prevents issues that could negatively affect customer relationships or regulatory requirements.
-
Enhanced User Experience
Validating functionality, usability, and performance ensures that the software aligns with user expectations. Through usability, performance, and functional validation, testing enhances the user experience, leading to smoother interactions and higher user satisfaction.
Quality Assurance
-
Improved Product Quality
Through built-in quality checks across workflows, QA testing enables products and services to meet or exceed expected standards. This leads to higher reliability, fewer production defects, and more substantial alignment with customer expectations, thereby enhancing the overall value delivered by the software.
-
Reduced Costs and Wastage
By identifying issues early in the development lifecycle, QA helps prevent defects from escalating into major problems later. This reduces rework, lowers support and return costs, and eliminates wasted effort, ultimately saving money and improving resource efficiency.
-
Consistency in Processes
QA creates and enforces clear standards, documentation, and procedures that teams follow consistently. This process consistency reduces output variability, improves predictability, and makes it easier to scale operations, onboard new staff, and maintain quality across products and releases.
-
Compliance with Standards and Regulations
Quality Assurance helps enterprises ensure their processes and products adhere to international quality standards and industry regulations. In addition to facilitating market expansion and boosting trust in governance and oversight procedures, compliance protects businesses from government-imposed fines.
Types of Software Testing and Quality Assurance
-
API Testing Services
API testing services help verify the functionality, reliability, security, and performance of application programming interfaces that enable system-to-system interaction. The testing services ensure that APIs function properly when processing requests and responses, handling authentication, and handling errors, while maintaining data accuracy. API testing services are a crucial component of contemporary enterprise systems because they help verify third-party system integrations, identify buggy dependencies, and prevent failures that could affect applications.
-
Automated Testing Services
The automated testing services use tools and platforms such as Selenium, Appium, and Katalon to run tests efficiently. Automation of testing helps accelerate testing cycles, reduce manual effort, and maximize test coverage across features and environments. Running automated tests on builds helps enterprises quickly identify regressions, supports continuous integration, and helps maintain quality during frequent releases.
-
Database Testing Services
Database testing services ensure the accuracy, integrity, and consistency of data stored in databases. Database testing services validate database schemas, queries, transactions, and stored procedures to ensure data is handled correctly during insert, update, delete, and migration operations. It also helps identify performance issues, deadlocks, and data inconsistencies.
-
Functional Testing Services
Functional testing validates that software works as expected based on the business requirements and use cases. It examines the software’s functionality through all the user interfaces, APIs, databases, security features, and processes. Functional testing services verifies that functions perform correctly across different scenarios, helping companies ensure that the software meets both technical standards and business requirements before going live.
-
Manual Testing Services
By analyzing software through its basic functionality and user interaction, manual testers can evaluate its effectiveness (functional correctness and usability). During manual testing, testers will review applications to identify edge cases and issues that automated testing may miss. Manual test services are often used in exploratory testing to validate user interface elements, explore all test paths and cases that require human judgment to verify that the application has met a user’s requirements and expectations.
-
Mobile App Testing Services
iOS and Android applications are validated by mobile testing services to ensure consistent performance, usability, and functionality. Device compatibility, operating system versions, screen resolutions, and different network conditions are all tested. Mobile app testing services help identify issues with application responsiveness, navigation, and device behavior, enabling companies to deliver trustworthy mobile applications.
-
Performance Testing Services
Performance testing services evaluate how applications perform under normal, peak, and stress conditions. Using techniques such as load, stress, and endurance testing, these services identify performance bottlenecks, response-time issues, and scalability limitations. Performance testing ensures applications are responsive, stable, and sufficiently robust to withstand real-world conditions without degrading or failing.
-
Security Testing Services
Security Testing Services help identify vulnerabilities that may allow unauthorized users to access an application or site, thereby exposing the application, the site, and the organization. Security testing evaluates authentication, authorization, data protection, and attack vectors to safeguard sensitive data, maintain compliance, and preserve application integrity and confidentiality.
-
Usability Testing Services
Usability testing services evaluate an application’s ease of use by analyzing navigation, layout, accessibility, and user experience. By improving usability, organizations can increase adoption rates, enhance satisfaction, and ensure applications are intuitive and efficient for their intended audience.
| Testing Type | Primary Focus | Key Purpose | Enterprise Value |
|---|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Difference Between White Box, Black Box, and Grey Box Testing Techniques
White-box, black-box, and grey-box testing are three core testing techniques used to validate software from different perspectives. Each approach focuses on a distinct level of system visibility and plays a specific role in ensuring application quality, security, and reliability.
White box testing is the process of understanding an application’s internal logic by giving testers complete visibility into the code. White-box testing is widely used in unit and integration testing to identify errors in code logic, security, and performance. White-box testing is a highly effective process for improving code quality, but it requires technical knowledge.
Black box testing is performed on the software solely from the perspective of user or system interaction, without knowledge of the internal code or design. The test engineers are concerned with inputs, outputs, and expected behavior as specified in the requirements. Black-box testing is commonly used in functional, system, and acceptance testing to verify that the application aligns with business and user expectations. Black-box testing identifies missing functionality, usability, and integration problems, but does not reveal internal code-related issues.
Grey box testing combines elements of both white-box and black-box testing. Testers have partial knowledge of the system’s internal workings, including architecture diagrams, database schemas, and API specifications. This approach allows for a more informed test design while still validating behavior from an external perspective. Grey box testing is beneficial for integration testing, security testing, and API validation in complex enterprise systems.
| Aspect | White Box Testing | Black Box Testing | Grey Box Testing |
|---|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Software and QA Testing Process
The software and QA testing process is a structured sequence of activities designed to ensure applications meet business, technical, and quality expectations before release. In enterprise environments, this process helps manage complexity, reduce risk, and maintain consistency across teams, systems, and delivery cycles.
1. Test Planning
The QA team will analyze business requirements, technical documents, and project objectives during this phase of testing to establish an overall testing strategy. In completing the overall testing strategy, the QA team will perform the following activities:
- Identify the scope of the testing
- Estimate how much time it will take run the tests
- Identify the types of testing, tools, and resources that will be used during the testing phase
By creating accurate test plans, development, QA, and business objectives will be aligned, and the plans will account for enterprise-specific factors such as compliance requirements and integration complexity.
2. Test Design and Preparation
During the test design and preparation phase, the QA teams develop test cases, scenarios, and data based on requirements, user stories, and system specifications. Otherwise, if your Test Environment has not been adequately prepared for Production, you might encounter issues when running tests in your Production Environment or when verifying it against real-world usage.
3. Test Execution
Test execution is the process of running manual and automated test cases to verify the functionality, performance, security, and usability of applications. At this point, test execution in enterprise environments spans multiple cycles and environments to ensure overall system stability. At the same time, defects are documented with details such as severity, priority, and reproduction steps.
4. Defect Reporting and Tracking
Defect reporting and tracking are vital for documenting and communicating discovered defects in a structured manner. Testers use defect-reporting and tracking tools to report defects, including detailed information such as descriptions, screenshots, logs, and steps to reproduce. Once the defects are analyzed, they are given to the development team for closure. Efficient defect tracking, coupled with maintenance, enables defect resolution and closure within agreed timelines. In most systems, defect tracking is used to prevent unrepaired defects from affecting the release or production environment.
5. Retesting and Regression Testing
Once defects are fixed, retesting is performed to confirm that the issues have been resolved correctly. Regression testing ensures that new changes have not introduced bugs into the existing processes. This is a critical phase, especially in an agile, continuous-delivery setup, where multiple changes occur regularly. Regression testing plays a vital role in maintaining stability within enterprise systems with complex dependencies.
6. Test Reporting and Closure
The closing stage involves gathering test results, coverage information, defect metrics, and quality insights to confirm that testing objectives are met before release. Test closure also includes documenting lessons learned, test artifacts, and opportunities for improvement in future cycles. In enterprise environments, this report supports informed decision-making, audit readiness, and continuous enhancement of testing processes.
A well-defined software and QA testing process enables enterprises to deliver stable, secure, and high-quality software with greater confidence and predictability.
Testing Methodologies and Approaches
Testing methods and techniques describe the approach, timing, and purpose of testing across the software development lifecycle. In enterprise environments, testing is not limited to execution; it also includes development environments, testing phases, and business critical functions.
1. Core Testing Methodologies
These methodologies define when testing is introduced and how it aligns with development activities.
-
Agile Methodology
Agile testing is an iterative and continuous process that takes place in short development cycles called sprints, where testing begins early and runs in parallel with development. As requirements change, testing also evolves to provide quick feedback, identify bugs early, and enable continuous improvement through frequent enterprise releases.
-
Waterfall Methodology
Waterfall is a sequential model of software development, where each phase is carried out in sequence, with testing performed only after development. This model of software development is most appropriate for projects with defined, stable requirements, structured documentation, timelines, and validation.
-
V-Model (Verification and Validation)
The V-Model extends the Waterfall model, with each development phase matched to a testing phase, ensuring verification and validation activities are planned early. By aligning development and testing phases, the model improves traceability, reinforces validation practices, and suits enterprise systems that demand strict compliance and quality control.
-
DevOps and Continuous Testing
With the advent of DevOps and continuous testing, automated tests are incorporated into the CI/CD process to support testing across the various phases of development and deployment in the enterprise, improving quality and speed.
-
Spiral Model
The Spiral model follows an iterative, risk-driven development process, with testing conducted in each iteration to identify, evaluate, and mitigate technical and business risks. This model, which incorporates both iterative development and risk management, is most suitable for large, complex business-related projects, where needs are subject to constant change, and risks must be closely monitored.
2. Levels of Testing
Levels of Testing provide an organized process for validating software quality through staged testing, where all aspects of individual components of the completed software are tested before testing the entire system. Performing staged tests allows defects to be separated from the overall product before any production-level releases.
- Unit Testing is the first level of testing and focuses on validating individual functions, methods, or components in isolation. It is typically performed by developers to ensure that each unit of code behaves as intended. Unit testing helps detect logic errors early, reduces debugging effort later, and provides a stable foundation for higher-level testing.
- Integration Testing verifies that different modules or components work correctly when combined. Once individual units are tested, integration testing verifies data flow, interfaces, and component interactions. This level helps identify communication issues, dependencies, or data inconsistencies that may not appear during unit testing.
- System Testing evaluates the fully integrated application as a complete system. It validates end-to-end functionality, performance, security, and usability against defined requirements. System testing ensures that the software operates correctly in an environment that closely resembles production conditions.
- Acceptance Testing is the final level of testing and confirms that the software meets business and user requirements. It often includes User Acceptance Testing (UAT), where stakeholders or end users validate real-world scenarios. Acceptance testing determines whether the application is ready for deployment and business use.
Best Practices
The best practices in software testing and quality assurance help enterprises deliver secure, reliable, and scalable software by embedding quality throughout the development lifecycle and aligning testing with business objectives, even during rapid release cycles.
Key best practices include:
- Integrate tests into CI/CD pipelines to enable continuous validation and faster feedback.
- Mix manual and automated testing to keep pace with speed and scope, while ensuring adequate consideration of usability.
- Involve QA early in the lifecycle to identify requirement gaps and prevent defects before development begins.
- Standardize testing processes and documentation to maintain consistency across teams and projects.
- Encourage collaboration across teams by aligning developers, testers, and business stakeholders on quality goals.
- Automate regression tests as much as possible to ensure the uninterrupted operation of existing features, even when the code changes frequently.
Challenges
The handling of complex technology systems is a significant challenge for organizations, which includes internal systems, third-party APIs, cloud services, and legacy systems. Testing these systems comprehensively across the business is highly challenging because even a single system issue can affect others.
Another major challenge is the speed at which technology teams are developing. The introduction of Agile and DevOps methodologies has accelerated the pace of code changes and approvals, leaving little time for adequate testing. If testing isn’t automated and well prioritized, the technology team can quickly find themselves in a position of poor quality while still delivering new changes at a high frequency.
Test environments and data limitations also pose challenges, as creating production-like environments is resource-intensive, and inadequate test data can lead to incomplete validation or missed defects. Inconsistent environments increase the risk of issues surfacing after deployment.
Enterprises also face skills and resource gaps, as advanced testing techniques, automation tools, and performance or security testing require specialized expertise that can be difficult to scale across large teams.
Finally, managing test coverage and defect prioritization becomes increasingly complex at scale. With large applications and multiple releases, ensuring critical areas are adequately tested while avoiding redundant effort requires strong planning, metrics, and governance.
Addressing these challenges requires a strategic testing approach that combines process maturity, automation, skilled resources, and continuous improvement.
Tools Used for Software Testing and Quality Assurance
| Tool Name | Primary Purpose | Enterprise Use Case |
|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Conclusion
Software testing and quality assurance are no longer optional checkpoints in enterprise development; they are strategic enablers of reliability, scalability, and business continuity. As systems grow more interconnected and release cycles accelerate, organizations must shift from reactive defect detection to proactive quality engineering. By combining structured processes, intelligent automation, and continuous validation within DevOps pipelines, enterprises can reduce risk while sustaining delivery speed.
Looking ahead, the future of QA will be shaped by AI-driven testing, predictive defect analysis, self-healing test scripts, and hyper-automation across the software lifecycle. These advancements will enable teams to move from validation to anticipation, identifying risks before they impact production and optimizing quality in real-time.
For organizations aiming to stay ahead of this shift, Telliant Systems delivers enterprise-grade QA and testing solutions for modern business needs. A mature, future-ready QA strategy not only safeguards performance today but also builds the foundation for continuous innovation, stronger customer trust, and long-term digital growth.
(Revised Version 2026)
Global spending on digital transformation hit $2.58 trillion in 2025 and is expected to reach $3.9 trillion by 2027, making one reality clear: digital transformation is no longer optional. Organizations without a clear digital transformation strategy are already losing efficiency and competitive ground. Organizations that delayed modernization over the past few years are now facing higher costs, fragmented systems, and declining customer relevance.
Digital transformation (DX) refers to the strategic integration of digital technologies across business functions to improve operations, decision-making, customer engagement, and value delivery. What was once considered an innovative initiative is now a core business requirement. In this context, digital transformation strategy is no longer owned only by IT teams but has become a board-level priority.
As businesses face economic instability, complex regulations, and rapid AI developments, digital transformation should be seen as an ongoing strategic skill rather than a one-time project.
The Importance of Digital Transformation in 2026
In 2026, digital transformation is defined less by adoption and more by how well it is executed. Organizations are expected to work with connected platforms, real-time data, and automation-driven efficiency.
A scalable digital transformation strategy enables businesses to align technological investments with long-term business objectives.
Although the fundamental tenets of digital transformation have not changed, their influence has spread throughout the entire organization.
-
Improved Customer Experience
Customer expectations in 2026 are shaped by immediacy, personalization, and consistency across channels. Digital transformation enables organizations to unify customer data, automate engagement workflows, and deliver personalized experiences across web, mobile, and emerging digital platforms. For many organizations, enterprise digital transformation is critical to breaking down data silos and creating a single view of the customer.
-
Stronger Security and Data Governance
The increasing interconnectedness of digital ecosystems has made data governance and cybersecurity strategic priorities. A clear digital transformation strategy supports contemporary security frameworks like centralized identity management, zero-trust architecture, and compliance-ready systems. Enterprise digital transformation also lowers risk by replacing old infrastructure with modern platforms. These platforms support ongoing monitoring, threat detection, and meeting regulatory requirements across various industries and regions.
-
Faster and more reliable decision-making
Data-driven decision-making is no longer optional. Digital transformation enables organizations to consolidate data from multiple systems and convert it into actionable insights using advanced analytics and AI-assisted intelligence. By providing leadership teams with real-time dashboards, predictive models, and automated reporting in 2026, business digital transformation enables quicker reactions to operational risks, shifting consumer behavior, and market changes.
-
Higher Employee Productivity and Operational Efficiency
Workforces are becoming more hybrid and digitally equipped. Digital transformation streamlines internal procedures by reducing manual labor, improving system integration, and introducing intelligent automation across HR, finance, operations, and IT. By implementing a well-thought-out digital transformation strategy, businesses can increase tool availability, speed up processes, boost employee productivity, and simultaneously improve engagement and retention.
-
Sustainable Revenue Growth and Profitability
Digital transformation remains a key driver of revenue optimization and cost efficiency. Scalable platforms, automated processes, and data-led decision-making help organizations reduce operational overhead while unlocking new business models. By 2026, corporate digital transformation will be a significant factor directly facilitating the necessary agility, scalability, and long-term profitability.
Key Digital Transformation Trends Shaping 2026
Digital transformation in 2026 is clearly moving toward intelligence-led execution. Nearly 96% of CIOs have already used or plan to use AI and machine learning to support digital-first initiatives. This shows how deeply AI is now integrated into business transformation plans.
Beyond this shift, several structural trends continue to define how organizations approach digital transformation:
- An increase in the use of intelligent automation in key business operations
- Persistent use of modular and cloud-native technology architectures
- Increased emphasis on advanced analytics and unified data platforms
- Extension of remote-first and hybrid operating models
- Increased use of digital tools in customer and employee trips
What Defines a Mature Digital Transformation Strategy in 2026
As digital transformation evolves, the gap between adoption and maturity is more visible. Many organizations have implemented digital tools, but fewer have built systems that operate effectively on a scale.
A mature digital transformation strategy in 2026 is defined by the following characteristics:
1. Integration-First Architecture
Organizations move away from fragmented systems toward connected ecosystems. Enterprise applications, data platforms, and workflows are integrated to ensure consistent information flow across functions.
2. Real-Time Data and Operational Visibility
Organizations rely on real-time data pipelines and dashboards instead of delayed reporting. This supports faster decisions and improves responsiveness to operational and market changes.
2. Real-Time Data and Operational Visibility
Organizations rely on real-time data pipelines and dashboards instead of delayed reporting. This supports faster decisions and improves responsiveness to operational and market changes.
3. Cloud-Native and Modular Infrastructure
Scalability is a baseline requirement. Cloud-native architectures, supported by APIs and microservices, allows systems to evolve without disrupting core operations.
4. Embedded Intelligence Across Workflows
Advanced analytics and automation are integrated into business processes, supporting forecasting, customer interactions, risk detection, and operational efficiency.
5. Alignment Between Business and Technology Teams
Business and technology teams operate with shared goals. Technology investments are directly linked to measurable business outcomes.
6. Continuous Optimization and Adaptability
Transformation is treated as an ongoing capability. Organizations monitor performance, refine processes, and adapt to changing technologies and business needs.
Pro Tip
Before scaling any digital transformation initiative, validate how quickly data moves across systems. If access to insights is delayed or inconsistent, scaling will amplify those gaps rather than fix them.
From Strategy to Execution
In large-scale transformation initiatives, operational inefficiencies often stem from fragmented systems and limited visibility. In one such engagement delivered by Telliant Systems, addressing these challenges led to a significant improvement in how information was accessed and used.
- 80% faster visibility into case-level data through centralized dashboards
- Improved coordination across systems and workflows
- More consistent data access for teams handling high-volume operations
This highlights how improving data access and system integration can directly influence decision-making speed and operational clarity.
Conclusion
In 2026, digital transformation remains essential, as it directly affects how businesses operate, expand, and remain competitive. At the employment level, its consequences are becoming more noticeable. In fact, 57% of firms say digital efforts cause more workplace changes than cultural or physical ones. This highlights the need to embed digital capabilities deeply across processes and systems, rather than treating them as isolated projects.
A clear digital transformation strategy has become a core business discipline, aligning leadership priorities with execution and long-term growth. Organizations that approach transformation as a continuous effort are better positioned to improve productivity, manage complexity, and respond to market change.
Organizations today see cloud adoption not just as a technology upgrade, but also to accelerate innovation, modernize operations, and compete in a more digital marketplace through modern cloud technology capabilities. However, moving applications and data to the cloud, especially in environments that involve cloud app development, is still complex and operationally challenging. Without a clear strategy and a structured plan, organizations face risks like delays, budget overruns, and service disruptions.
A cloud migration roadmap is essential. It acts as a strategic framework to help transition from old infrastructure to a modern cloud environment. This process should be controlled and focused on delivering value while managing risks, resources, operational needs, and business goals.
This article presents a practical, step-by-step guide to building a cloud migration roadmap that connects technology initiatives with enterprise strategic priorities.
What is a Cloud Migration Roadmap
A cloud migration roadmap is a detailed plan outlining how an organization will migrate its applications, data, and computing workloads from legacy systems or on-premises environments to a new cloud environment. This process is carried out carefully and in an organized manner.
It sets clear goals, identifies priorities, assigns responsibilities, and outlines tasks and milestones. This structure allows teams to carry out migrations in a coordinated, predictable, and organized way.
At its core, the roadmap ensures that technical decisions support business outcomes such as cost optimization, improved performance, operational agility, and compliance.
Why a Lifecycle Perspective Is Critical to Cloud Migration
By moving tasks through planned stages, including assessment, planning, execution, stability, and optimization, a lifecycle approach sees cloud migration as an ongoing transformation program instead of a single event. This method guarantees clear business value throughout the migration process.
By viewing migration as a series of steps rather than a single significant technology change, organizations enable learning, flexibility, and ongoing improvement.

Step 1: Conduct a Thorough Assessment
The first and most critical step in a cloud migration plan would be to conduct a comprehensive assessment of the existing environment. Map dependencies, assess performance, and identify integration risks by creating an automated discovery list of servers, apps, databases, storage, networks, middleware, and connectors.
The emphasis should be on the dependency mapping to prevent errors during the migration phase. Review legacy systems for retirement or upgrades. Check licensing and support limits. Classify data based on regulatory needs and sensitivity.
The assessment should also consider skills availability across teams and identify capability gaps that may require training or external expertise. The result of this phase is a clear understanding of what exists today and what must be modernized, prioritized, or retired.
Step 2: Define Business Objectives and KPIs
Successful cloud migrations are driven by business outcomes rather than technology decisions alone. Your roadmap should clearly define why the migration is being undertaken and what value the organization expects to deliver.
Common objectives include:
- Reducing infrastructure and maintenance costs
- Increasing application performance and reliability
- Facilitating faster cycles of innovation and scalability
- Increasing security and adhering to regulations
- Assisting with new product capabilities and digital initiatives
These objectives should be measurable. Set key performance indicators. Include uptime targets, response-time thresholds, cost-reduction goals, and operational efficiency metrics. By clearly defining specific outcomes at the start, the organization makes sure that every migration decision delivers measurable business value.
Step 3: Establish Governance and Team Structure
Cloud migration demands careful planning and cross-departmental collaboration. A governance model should be developed that includes representatives from the Operations, Finance, Security, IT, and Business Leadership Departments.
Clearly state who is responsible for decision-making, risk management, expense monitoring, and confirming compliance. Team responsibility and coordination are ensured by hiring a qualified cloud transformation owner or migration program lead.
Governance checkpoints should be embedded throughout the roadmap to review alignment, progress, risk exposure, and cost performance.
Step 4: Select the Right Migration Strategy
At this stage, determine the most appropriate migration strategy for each workload or application. Not every system should be migrated in the same way.
Understanding the 7R Cloud Migration Strategies
1. Rehost
Rehost means that application workloads are moved to a cloud with minimal modifications. There is a copying of existing configurations or infrastructure patterns. The process increases migration speed while ensuring everything remains the same, with no changes required.
2. Relocate
Relocate moves entire workloads or virtual machines to a cloud provider’s infrastructure with few architectural changes. It uses cloud-hosted infrastructure while keeping existing configurations, operational processes, networking, and management models unchanged.
3. Replatform
Replatforming existing workloads by adding new platforms and features while retaining the workload’s primary architecture will improve performance, scalability, and compatibility with a cloud environment. This method allows for gradual modernization during workload migration while maintaining much of the technical debt associated with the workload.
4. Refactor
Refactor redesigns application components or code to use cloud-native structures, such as microservices and containerization. This change improves scalability, resilience, and maintenance. It also opens the door to better automation and long-term innovation.
5. Repurchase
Repurchase replaces SaaS or cloud-based platforms with options that have similar or improved features compared to outdated apps. This update reduces maintenance costs, simplifies licensing, and helps with modernization. It also makes it faster to use standard features.
6. Retire
Retirement removes old systems that no longer benefit the business. It eliminates assets to cut operational costs, reduce security risks, and reduce technical debt. This process also makes migration easier.
7. Retain
Retain keeps specific workloads or systems on-site or in hybrid environments because of latency, compliance, integration, or business needs. It supports coexistence while allowing surrounding services to use the cloud and creates options for future modernization.
This selective approach prevents unnecessary modernization efforts and ensures migration efforts are focused where they create the most business value.
Step 5: Plan Migration Phases and Prioritization
Instead of one big move, cloud migration should occur in planned stages. Workloads should be categorized into migratory waves based on their dependency, complexity, and importance. This approach lowers risk while ensuring that services continue to operate as intended.
A phased plan typically includes:
- Pilot program to test procedures and technologies for low-risk workloads.
- Phase of core migration for significant sequenced wave applications.
- Stabilization phase to monitor performance and fix any issues after migration.
- Optimization phase to improve cost, scalability, and operations.
Every stage should specify acceptance standards, testing checkpoints, rollback protocols, and entry and exit criteria. This reduces downtime and allows workloads to be moved in a predictable, orderly manner that aligns with business goals.
Step 6: Select Proper Tools and Automation
Migration speed, reproducibility, and robustness improve significantly with the right tools that enable consistent execution and reduce manual effort. Automated testing, environment replication, data synchronization, dependency discovery and mapping, CI/CD pipelines, Infrastructure-as-Code, process orchestration, rollback validation, configuration management, performance testing, monitoring, and logging should all be supported by these tools.
Functions such as automated configuration management, pipeline-based deployments, and infrastructure-as-code help minimize manual intervention and ensure consistency. Further, it provides assistance with rewind functionality, validation, and quick fixes in case unforeseen issues occur during migration.
Step 7: Integrate Security and Compliance
Security and compliance need to be part of the roadmap from the start; they should not be added later.
Key security activities include:
- Classifying data and mapping regulatory obligations.
- Defining encryption for data in transit and at rest.
- Implementing identity and access management policies.
- Establishing logging, monitoring, and incident response workflows.
Integrating security early reduces rework, minimizes operational risk, and strengthens organizational trust in the migration process.
Step 8: Execute Migration and Validate
After setting up the planning and governance structure, migration execution begins in accordance with the migration phase plan.
These validation activities include:
- Testing applications’ functions in the operational environment.
- Benchmarking of Performance on Pre-Migration Bases.
- Verification of security and access controls.
- User Acceptance Testing & Operational Readiness Review Responsibilities
Rollback plans must be prepared for every migration to maintain business continuity in the face of unexpected failures.
Step 9: Post-Migration Optimization and Continuous Improvement
Post-migration optimization ensures workloads run well in the cloud. It also helps them operate efficiently, securely, and without wasting money. After stabilization, organizations should review performance metrics, resource use, and workload behavior. This will help identify chances for improvement, such as adjusting instance sizes, fine-tuning autoscaling policies, increasing storage efficiency, and modifying network setups.
Cost governance should be reinforced through monitoring, budgeting controls, and usage analysis. Security controls, access policies, and compliance requirements must be reassessed in the new environment.
Continuous improvement enables teams to modernize further, adopt cloud-native services, strengthen cloud technology capabilities, and enhance reliability and long-term business value.
From Planning to Execution: Realizing the True Value of Cloud Migration
A cloud migration roadmap is an essential strategic instrument that guides an organization through a complex transformation journey. By using a straightforward, lifecycle-driven method, organizations can reduce risk, manage costs, maintain operational continuity, and gain ongoing business value from cloud adoption.
At Telliant Systems, we help enterprises architect, plan, and execute cloud migration programs that align technology modernization with business outcomes. Our consulting and engineering teams work closely with organizations to design migration roadmaps that are practical, measurable, and tailored to their strategic priorities.
Digital platforms have become an essential part of everyday life, allowing people to access services, information, education, healthcare, and financial systems online. However, many websites are still difficult to use for individuals with visual, auditory, cognitive, or motor impairments. When websites are not developed with accessibility in mind, users with assistive technologies, such as screen readers, face difficulties accessing the content.
This is why many organizations are working to ensure WCAG compliance, ensuring their platforms are accessible to and usable by all. These are well-known website accessibility guidelines that help organizations create websites that are usable across different platforms and technologies. Improving web accessibility compliance benefits people with disabilities and enhances usability for all.
1. What Is WCAG?
The Web Content Accessibility Guidelines (WCAG) are standards for accessible digital products and services, developed by the World Wide Web Consortium (W3C), specifically through its Web Accessibility Initiative (WAI). Organizations seeking WCAG conformance adhere to these WCAG accessibility guidelines to make digital products and services accessible to users with different physical, mental, and sensory limitations.
The WCAG accessibility standards are generally applicable to a range of digital spaces and technology infrastructures.
They are relevant for:
-
Websites
Public portals and e-commerce websites must adhere to WCAG guidelines to ensure that users with disabilities can access and use their services.
-
Web Applications
Interactive applications such as dashboards, SaaS platforms, and enterprise software must follow WCAG accessibility guidelines to ensure accessibility across complex user interfaces and dynamic components.
-
Mobile Applications
Mobile applications on devices such as smartphones and tablets need to be WCAG-compliant so that the user interface and content are easily usable with screen readers and accessibility settings.
-
Digital Platforms
Government portals, learning platforms, and digital service ecosystems often enforce WCAG compliance requirements as a baseline requirement for inclusive user experiences.
2. Understanding WCAG Versions
Driven by advances in technology and accessibility research, WCAG continues to introduce updates that support organizations in improving accessibility and managing new digital accessibility challenges. The evolution of accessibility guidelines is important to ensure that various digital platforms and complex user interfaces are accessible across various devices and assistive technologies.
The major versions of WCAG include the following:
-
WCAG 1.0 (1999)
The first official version of the guidelines introduced foundational accessibility concepts for early web environments. WCAG 1.0 primarily focused on static HTML content and specified checkpoints to enhance accessibility for screen readers and assistive technologies available at the time. Although this version is historically important, it has become obsolete with the introduction of modern web applications and content frameworks.
-
WCAG 2.0 (2008)
WCAG 2.0 provided a technology-independent model expected to accommodate evolving web technologies and interactive digital media. It defined the fundamental accessibility principles of Perceivable, Operable, Understandable, and Robust, which are still used to define modern accessibility guidelines in WCAG. Many international accessibility regulations still reference WCAG 2.0 as a baseline framework for website accessibility standards.
-
WCAG 2.1 (2018)
The release of WCAG 2.1 expanded the existing framework to address accessibility challenges associated with mobile devices, touch interfaces, and low vision users. Organizations that want to follow the WCAG guidelines can take advantage of the new WCAG 2.1 accessibility guidelines for mobile devices, keyboards, and assistive technologies.
-
WCAG 2.2 (2023)
The latest update includes guidelines to improve the accessibility of digital content for users with cognitive disabilities and complex interaction patterns. Achieving WCAG 2.2 Compliance has introduced new requirements that improve the usability of navigation and authentication, and the accessibility of the interactive interface, making it stronger than the WCAG Compliance requirements for the latest digital platforms.
4. Benefits of WCAG Compliance
Some benefits for organizations that use digital platforms in their businesses and attain WCAG compliance include improved user interface, user experience, and customer satisfaction. Organizations that adopt website accessibility standards can reach a wider audience than those that do not, as individuals with disabilities can interact with digital content more effectively.
Organizations are also focusing on web accessibility compliance because improving accessibility has been shown to positively impact mobile usability, search engine optimization, and the overall clarity and consistency of the user interface. In addition, meeting established WCAG compliance requirements helps organizations reduce legal risks associated with accessibility lawsuits and regulatory violations in jurisdictions that require accessible digital services.
4. The Four Core WCAG Principles
The entire WCAG model is based on four basic principles for accessible design for users with disabilities.
-
Perceivable
Digital content must be made available to users through the senses they can perceive. For example, images should include alternative text, videos should include captions, and text should have good color contrast so users with low vision can easily read it. Following these practices supports inclusive design and helps organizations meet modern WCAG accessibility standards.
-
Operable
The interfaces should enable the user to interact with navigation elements and functionality using various input methods, such as the keyboard, voice commands, and assistive technology. All interactive elements, such as menus, forms, and buttons, should be accessible via the keyboard, enabling users to use the website effectively without a mouse and ensuring WCAG compliance.
-
Understandable
Information and user interface behavior must be predictable, readable, and logically structured so that users can easily understand digital interactions. Users should be able to complete tasks easily through clear form instructions, predictable interface behavior, and meaningful error messages, which align with established WCAG accessibility guidelines.
-
Robust
The digital content must be compatible with assistive technologies and new web browsers, allowing the user to access the information on various devices and environments. Using appropriate HTML structure, accessible coding, and screen reader components will ensure long-term accessibility and usability of the content and its alignment with the WCAG accessibility guidelines.
5. WCAG Conformance Levels
WCAG defines three conformance levels that indicate the degree to which a website satisfies accessibility success criteria defined in the guidelines.
| Conformance Level | Description | Accessibility Impact |
|---|---|---|
|
|
|
|
|
|
|
|
|
Most organizations aim for Level AA because it satisfies widely accepted website accessibility standards while maintaining practical development feasibility.
6. Common WCAG Compliance Issues
- Images that lack alternative text are not read to users with visual impairments by screen readers.
- Poor contrast between text and background makes it difficult for users with low vision to read the content.
- Navigation elements that cannot be accessed through keyboard input create barriers for users who rely on assistive devices.
- An improper heading structure makes it difficult for screen readers to interpret the page hierarchy correctly.
- Forms without clear labels or instructions prevent users from completing tasks effectively.
- Buttons and links without descriptive labels confuse screen readers and reduce accessibility.
Pro Tip:
To maintain compliance with the Web Content Accessibility Guidelines, organizations should integrate accessibility testing into their regular development workflow. Teams can use tools such as axe DevTools, WAVE, and Lighthouse to identify accessibility issues early and ensure that websites remain aligned with WCAG requirements as new features and updates are introduced.
7. How to Test a Website for WCAG Compliance
Testing accessibility requires a combination of automated tools, manual testing procedures, and assistive technology validation methods. Automated accessibility scanners help identify structural issues such as missing alt text, color contrast violations, and invalid HTML attributes that may affect WCAG compliance. However, automated testing alone cannot identify every accessibility problem because some usability issues require human evaluation.
Manual testing plays a critical role in validating navigation, interactive components, and user workflows across different accessibility scenarios. Accessibility specialists often test keyboard navigation, screen reader compatibility, and focus management to ensure full compliance with web accessibility standards.
The use of automated scanning, usability evaluation, and accessibility audit helps organizations comply with changing WCAG guidelines and requirements.
8. How to Achieve WCAG Compliance
- A comprehensive accessibility audit must be conducted to assess the website’s compliance with WCAG accessibility standards.
- The accessibility issues must be identified, and the remediation activities for the website’s design and development components must be prioritized.
- The website’s color contrast, navigation, form, and keyboard accessibility also require enhancement.
- A structured WCAG compliance checklist should be followed to facilitate accessibility implementation across all pages and features of the website.
- Accessibility testing should be conducted to ensure compliance with all WCAG guidelines.
- Accessibility practices should be incorporated into design and development processes to ensure long-term compliance with web accessibility guidelines.
9. WCAG Compliance and Legal Regulations
Across global accessibility regulations, WCAG is widely referenced as the primary guideline, and government agencies and courts often require organizations to demonstrate compliance when evaluating websites. In the United States, accessibility lawsuits often reference WCAG success criteria when interpreting requirements under the Americans with Disabilities Act.
Similarly, the European Union Web Accessibility Directive requires public sector websites to adhere to internationally accepted accessibility standards, such as those set out in the WCAG guidelines. Many jurisdictions require compliance with WCAG 2.1 or WCAG 2.2 as a component of their digital accessibility regulations and policies. Following these internationally accepted WCAG accessibility guidelines helps organizations reduce legal risk while ensuring accessible digital services.
10. Best Practices for Accessible Website Design
- Incorporate inclusive design principles early in the product development cycle to achieve better accessibility outcomes.
- Use clear typography, proper color contrast, and a consistent layout to facilitate accessible navigation.
- Make sure that all forms, menus, and buttons have descriptive labels and provide focus indicators.
- Organize headings properly so that assistive technologies can understand the page hierarchy.
- Include captions and transcripts of multimedia content to facilitate users with hearing disabilities.
- Adhere to contemporary accessibility guidelines from WCAG to ensure continued compliance with accessibility standards.
11. Maintaining WCAG Compliance Over Time
Accessibility should be considered an ongoing operational activity rather than just a one-time compliance activity. As websites are updated and new features are added, along with design and content updates, accessibility problems may creep back in without proper governance mechanisms in place. It is recommended that periodic audits of websites be conducted to ensure compliance with updated accessibility guidelines and to prevent problems that have been resolved earlier from creeping back into the websites.
Continuous monitoring tools can be used to identify accessibility issues and support ongoing WCAG compliance. It is also important to use accessibility testing to ensure that new code does not break WCAG compliance requirements during continuous integration. Maintaining alignment with evolving standards, such as WCAG 2.2 compliance, ensures that digital platforms remain inclusive as technology and accessibility research continue to advance.
12. Conclusion
Accessibility is no longer a niche technical concern but a fundamental aspect of inclusive digital experiences. Organizations adopting a structured accessibility approach aligned with WCAG can now build platforms that remain accessible to a broader audience. By using the WCAG compliance method, organizations can not only ensure usability but also avoid legal risks and align with international website accessibility standards.
Businesses that integrate accessibility into design systems, development workflows, and quality assurance processes achieve stronger long-term web accessibility compliance. As digital ecosystems continue evolving, following established WCAG accessibility guidelines and meeting defined WCAG compliance requirements will remain essential for organizations committed to equitable and inclusive digital access.
While the adoption of digital technology has made data more accessible, it has also led to data fragmentation across systems that lack standardized communication protocols. This creates significant barriers to seamless healthcare data exchange across clinical, administrative, and patient engagement platforms.
Healthcare Interoperability enables clinical and non-clinical data to move securely across applications, systems, and institutional boundaries without compromising context, accuracy, or compliance requirements. In the absence of an effective data integration framework, healthcare providers are likely to face delayed diagnoses, repeated procedures, incomplete patient records, and inefficient administrative processes, all of which impact patient outcomes and organizational performance.
Levels of Interoperability in Healthcare Integration
Healthcare Interoperability is structured across multiple operational levels that determine how healthcare data exchange occurs between systems and how effectively that data is interpreted and utilized across integrated digital health environments.
-
Foundational Interoperability
Foundational interoperability enables data exchange only, not communication that assumes a usable structure. It does not guarantee processing or usability, but it ensures connectivity between the integrated platforms.
-
Structural Interoperability
This level standardizes the format, syntax, and organization of exchanged data so that information fields remain consistent and properly aligned during transmission between systems.
-
Semantic Interoperability
This level maintains the meaning and context of the transmitted data, enabling the receiving application to correctly interpret medical terminology, diagnoses, and treatments without requiring manual interpretation.
-
Organizational Interoperability
This level incorporates governance policies, regulatory frameworks, and workflow alignment to support coordinated Healthcare Integration across institutions, payer networks, and care-delivery environments.
Each interoperability level strengthens Data Integration by supporting accurate, compliant, and scalable healthcare data exchange across interconnected healthcare systems.
Evolution of Healthcare Data Exchange Standards
As healthcare technology adoption increased, the need for standardized messaging protocols became essential to support interoperability across heterogeneous environments. Health Level Seven (HL7) was introduced as a set of international standards for the structured exchange of clinical data between healthcare applications. HL7 Version 2 supports standardized messaging for transmitting patient admission data, laboratory results, discharge summaries, and billing information, while HL7 Version 3 improves semantic interoperability through a more structured data modelling approach.
Clinical Document Architecture is an HL7 standard that enables the representation of electronic clinical documents using a common framework. Traditional HL7 implementations relied on message-based integration, which required custom interface engines and manual data mapping to maintain interoperability across systems.
HL7 for Healthcare Data Integration
HL7 continues to play a foundational role in Healthcare Interoperability by enabling message-driven communication between clinical systems that operate within hospital networks and enterprise healthcare environments. The HL7 architecture is based on structured message segments that represent patient demographics, diagnostic results, medication orders, treatment plans, and administrative information.
Healthcare organizations frequently use HL7 messaging for integrating electronic health record systems with laboratory platforms, radiology imaging systems, pharmacy databases, and billing applications.
Common HL7 message types that support healthcare data exchange include:
- Admission Discharge Transfer messages
- Order Entry communications
- Observation Reporting messages
Maintaining consistent data integration across evolving healthcare infrastructures often requires dedicated interface management strategies that ensure message integrity and semantic consistency.
FHIR for Modern Healthcare Integration
FHIR represents a significant advancement in healthcare integration by enabling API-driven healthcare data exchange through a resource-based architecture that aligns with modern web standards. Contrary to the use of message-oriented communication, FHIR breaks down clinical data into modular resources like patient records, medications, diagnostic results, procedures, and care plans that can be retrieved via RESTful APIs.
FHIR also supports common data formats, including JSON and XML, which allow healthcare developers to more easily build bridges between clinical systems, mobile health apps, cloud platforms, analytics systems, and remote monitoring devices. This approach enhances interoperability across distributed healthcare ecosystems by enabling real-time data retrieval and scalable deployment across enterprise environments.
Healthcare organizations implementing FHIR-based data integration can improve patient engagement initiatives, streamline care coordination workflows, and support advanced analytics capabilities that rely on consistent clinical datasets.
HL7 vs FHIR: Comparative Analysis
Both HL7 and FHIR contribute to Healthcare Interoperability by addressing different integration requirements across healthcare environments. HL7 remains suitable for internal enterprise messaging, while FHIR supports modern application-level integration across cloud-based ecosystems and patient-facing platforms.
Healthcare Data Integration Architecture in Practice
Healthcare Interoperability in the enterprise world relies on a structured Data Integration architecture that supports standardized healthcare data exchange between legacy and new healthcare systems. Interface engines or integration middleware facilitate HL7 message routing, transformation, and connectivity between electronic health records, lab systems, radiology systems, and billing systems.
API gateways that provide secure access to clinical resources from mobile apps, cloud analytics platforms, and remote monitoring devices enable healthcare integration with FHIR. Data transformation layers enable compatibility between FHIR resources and HL7 messaging formats, and Master Patient Index systems enable appropriate patient identity resolution.
Implementation Challenges in Healthcare Interoperability
Healthcare organizations pursuing enterprise-wide healthcare integration often encounter technical and operational barriers that affect data integration outcomes. Legacy clinical systems may lack support for modern interoperability standards, requiring additional middleware or interface engines to enable healthcare data exchange across applications.
Semantic inconsistencies between data models may introduce interpretation errors, while the need for data privacy and security, as mandated by regulations, requires the enforcement of governance policies during interoperability. Scalability in integration may also become an issue as healthcare organizations increase their digital health services across various facilities.
To address these issues, there is a need for implementation strategies that incorporate technical architecture with compliance and organizational goals.
Best Practices for Scalable Healthcare Data Exchange
Healthcare providers seeking to implement sustainable Healthcare Interoperability initiatives should consider the following best practices to ensure scalable and secure healthcare data exchange.
- Adopt standards-based Healthcare Integration strategies that emphasize scalability, data management, and compatibility.
- Use middleware tools to enable message processing and routing in a multi vendor environment.
- Implement API gateways to facilitate secure interactions between FHIR-enabled applications.
- Invest in semantic data normalization infrastructure to guarantee a common understanding of clinical data by integrated systems.
- Continuously evaluate interoperability performance and manage version updates of integration standards.
- Foster collaboration among stakeholders in IT and clinical domains to facilitate collective data integration efforts.
By integrating HL7 messaging with FHIR APIs, healthcare organizations can create an interoperability framework that is adaptable and innovative.
Conclusion
Healthcare Interoperability is a crucial requirement for secure, scalable data exchange across current healthcare and administrative use cases. HL7 and FHIR enable healthcare integration by supporting both legacy messaging requirements and API-based data integration. HL7 facilitates structured communications between enterprise applications while FHIR allows for real-time interoperability between applications hosted in the cloud, analytical systems, and other healthcare-related application; this was achieved by organizations using a standardized integration approach based on HL7 and FHIR to optimize their operations, meet regulatory compliance requirements, encourage greater involvement from patients in their own care, and create a sustainable data exchange.
The New Reality of Healthcare Software
Healthcare software development has moved far beyond basic digitization of patient records and administrative processes. Modern healthcare organizations use application software to store large volumes of patient information; this software enables providers to make decisions and collaborate with other organizations in real time. As healthcare providers deliver care to patients through electronic and physical channels, software also plays a significant role in patient safety, operational efficiency, and regulatory compliance.
The growing reliance on digital systems has also heightened the risks to healthcare data security. Cyber-attacks target Healthcare Organizations frequently because of the sensitive nature of their protected health information and its long-term value. Therefore, a secure method of developing applications involving the Healthcare Organization must encompass many areas beyond just perimeter-based security. It must also include the application’s Infrastructure, Application Logic/Data, storage, and Integration layers.
At the same time, healthcare interoperability has become a foundational requirement rather than a future goal. The effectiveness of clinical outcomes, care coordination, and patient experience now depends on how accurately and efficiently systems exchange data across organizational and technical boundaries.
Several industry-wide shifts are transforming the design and deployment of modern healthcare software platforms.
- The rapid expansion of digital health platforms, telemedicine solutions, and mobile applications requires secure healthcare application development to ensure safe access to patient data across multiple environments and devices.
- The industry-wide push for standardized data exchange via FHIR and HL7 integration enables consistent communication among electronic health records, laboratories, imaging systems, and external partners.
- The growing complexity of healthcare system integration occurs as organizations connect cloud-native platforms with legacy clinical systems, medical devices, and health information exchanges.
Changing industry demands have altered expectations for healthcare software platforms, making it essential for performance, scalability, and usability to operate alongside strong security, compliance, and interoperability standards.
Software teams can no longer afford to prioritize speed or functionality over data protection or integration readiness. In the current healthcare landscape, software must be designed around a security-first architecture and interoperability to support resilient, compliant, and adaptable healthcare systems.
Core Pillars of Modern Healthcare Software Architecture
Modern healthcare software architecture must support far more than functional requirements. To achieve this balance, successful healthcare platforms are built on a set of foundational architectural pillars that guide design decisions across every layer of the system.
Such architectural pillars serve as interconnected principles that shape how healthcare software development addresses security, interoperability, scalability, performance, and compliance.
1. Security-First Architecture
A security-first architecture places healthcare data protection at the center of system design rather than treating it as an afterthought. Given the sensitive nature of clinical and patient data, healthcare data security must be embedded into infrastructure, application logic, and data workflows from the earliest stages of development.
Security-first healthcare software architectures emphasize strong identity controls, secure data storage, encrypted communication channels, and continuous monitoring across all system components. This approach ensures that patient information remains protected as it moves between users, applications, and integrated systems, while also reducing the risk of breaches, unauthorized access, and operational disruptions.
2. Interoperable Design
Interoperable design enables healthcare systems to exchange data accurately, consistently, and in real time across internal and external platforms. To provide a coordinated approach to health care delivery and complete visibility into patient care, health care software platforms need to enable different types of software to communicate easily with one another, including electronic health records, laboratories, imaging, pharmacies, and other vendors and partners.
Creating a standard operating method with other software vendors through FHIR and HL7 interoperability enables healthcare organizations to break free from data silos and the limitations of legacy systems. An interoperable design ensures that healthcare system integration efforts remain scalable and future-ready, enabling the addition of new systems and partners without extensive reengineering.
3. Scalable Data Pipelines
Healthcare platforms generate and consume massive volumes of structured and unstructured data, including clinical notes and diagnostic results, device telemetry, and patient-generated health data. Scalable data pipelines are essential for managing this growth while maintaining data integrity, availability, and performance.
Scalable ingestion, processing, and storage mechanisms that can handle varying workloads without degrading service are essential to modern healthcare software architectures. These pipelines ensure secure data flows between linked systems and applications while supporting analytics, reporting, and clinical insights. applications.
4. High Performance and Reliability
Performance is crucial for all healthcare systems, as patient care outcomes can be affected by service interruptions or volatility. Healthcare software must deliver continuous responsiveness, be scalable to support multiple concurrent users, and be available during periods of high utilization.
Performance-focused designs prioritize efficient data access, optimized APIs, fault tolerance, and robust infrastructure design. This guarantees that, as system complexity and usage continue to rise, clinicians, administrators, and patients can rely on healthcare applications for prompt access to vital information.
5. Compliance by Design
Instead of addressing regulatory requirements through manual workflows or post-deployment audits, healthcare software teams that adopt a compliance-by-design approach integrate them directly into the architecture. For healthcare platforms, this includes building HIPAA-compliant software that enforces privacy, access control, auditability, and data protection across all components.
Healthcare software developers can reduce risk and make compliance easier by integrating compliance into their products’ workflows, access methods, and database management processes. Through Compliance by Design, these products can continue to evolve with changes in compliance requirements without requiring substantial architectural changes.
A Security-First Approach to Healthcare Software Development
Ransomware attacks, credential abuse, and data leakage across interconnected systems are just a few of the many security risks that healthcare businesses must address. Healthcare software must adhere to a well-organized, defense-in-depth strategy to safeguard patient data and maintain regulatory compliance. A workable approach for enhancing healthcare data security while promoting interoperability and operational resilience is outlined in the ten steps that follow.
1. Apply HIPAA Technical Safeguards by Design
To comply with HIPAA Technical Safeguards, modern healthcare platforms should integrate technical safeguards for access control, authentication, system activity logging, and protection of electronic transmission into their system architecture. Hence, these protections work the same way across all applications and integration components, and there is no need for manual interfacing with them.
2. Encrypt Data at Rest and in Transit
To protect sensitive health information, robust encryption rules must be used. To ensure confidentiality and integrity, data stored in databases, file systems, and backups should be encrypted at rest using AES-256, and healthcare data transmitted between systems should be protected in transit using TLS.
3. Implement Role-Based Access Control
Role-based access control ensures that users can access only the data required for their responsibilities. Clinical staff, administrators, and support teams should have clearly defined permissions that enforce the principle of least privilege across all healthcare systems.
4. Enforce Multi-Factor Authentication
Multi-factor authentication (MFA) helps confirm a user’s identity by requiring more than just a password. This change significantly reduces the likelihood of unauthorized access, even if passwords are stolen, across healthcare systems and applications spread across multiple systems.
5. Centralize Identity and Access Management
Identity and access management (IAM) systems unify authentication, authorization, and user lifecycle management across healthcare platforms. IAM ensures that users, applications, and devices are granted the right level of access at the right time and for the right purpose.
6. Maintain Audit Trails and Activity Logging
When using healthcare software to access data and modify systems, there must be sufficient record-keeping through an activity log to support audits and investigations if needed. This type of record-keeping provides accountability and enables real-time security measures to monitor the overall actions being recorded.
7. Adopt a Zero-Trust Architecture
The Zero-Trust architecture eliminates the implicit trust that exists in healthcare environments. Every access request is constantly validated based on identity, context, and policy, thus minimizing the threat of lateral movement and the resulting damage from compromised users or devices.
8. Secure APIs and Data Exchange Layers
Interoperability depends on APIs and integration layers that must be secured through authentication, authorization, rate limiting, and input validation. Secure APIs protect data integrity and confidentiality while enabling safe integration into healthcare systems.
9. Establish Backup and Disaster Recovery Controls
Healthcare organizations need to ensure they maintain secure, tested backups of their data that are isolated from production systems. Organizations should also establish disaster recovery plans that define recovery objectives and procedures for restoring operations following disruptive events such as system failures or cyberattacks.
10. Prepare for Ransomware and Incident Response
To prepare for ransomware and respond to incidents, healthcare organizations must be proactive by monitoring their systems, segmenting them, documenting incident response plans, and defining escalation paths, communication procedures, and recovery procedures. These procedures help healthcare organizations minimize disruption to patient care in the event of a malware incident.
Interoperability: The Backbone of Connected Care
Healthcare systems are becoming increasingly interconnected, making it essential for healthcare development companies to include interoperability features across all their software applications. The seamless transfer of information between systems (e.g., hospitals, clinics, labs) and across multiple care settings (e.g., hospital-to-home) is critical to patient care and overall patient health.
As healthcare environments expand to include cloud platforms, third-party applications, and remote care technologies, interoperability must be treated as a core architectural capability rather than a point-to-point integration exercise.
Modern healthcare platforms must support standardized data exchange while maintaining healthcare data security and regulatory compliance. This balance is critical because interoperability often involves sharing protected health information across organizational and technical boundaries. Thus, integration of healthcare systems needs to be carefully planned to facilitate safe, traceable, and standards-compliant communication at all points of care.
FHIR APIs and Modern Data Exchange
With the modernization of the healthcare platform, FHIR APIs enable scalable, resource-based access to clinical data using modern web standards. Through FHIR integration, healthcare applications can retrieve and exchange patient records, observations, medications, and clinical events in a consistent and machine-readable format. This approach simplifies integration across electronic health records, mobile applications, and external platforms while supporting real-time data access.
Similarly, FHIR interoperability plays a significant role in developing secure healthcare applications. This is because FHIR APIs, when properly implemented, provide a simple, scalable integration solution with robust security policies. Furthermore, FHIR interoperability ensures secure API-based communication through standardized data models.
HL7 Messaging and Legacy System Connectivity
The need for HL7 messaging as a link between outdated healthcare systems and for event-driven communications related to admissions, discharges, lab results, and clinical data is critical, as the healthcare market continues to migrate towards an API-based FHIR architecture. HL7 messaging is widely used in healthcare to connect outdated systems with emerging technologies.
To maintain continuity in healthcare service delivery, software providers can offer an evolutionary path to a modernized infrastructure that leverages existing applications while supporting integration with legacy systems via FHIR APIs and HL7 messaging.
SMART on FHIR for Secure App Ecosystems
Based on FHIR standards, SMART on FHIR provides a secure, reliable launch and authorization process for applications running on EHR systems. It provides a mechanism for third-party clinical applications to access patient data through standardized authentication and authorization securely.
In addition, the use of SMART on FHIR supports the development of innovative healthcare solutions by establishing secure, interoperable application marketplaces that meet HIPAA-compliant software requirements and protect patient privacy.
Integration Across Core Clinical Systems
To achieve effective healthcare interoperability, seamless integration across core clinical systems, such as EHRs, LIS, RIS, PACS, and pharmacy systems, is needed. These systems manage different aspects of patient care, and interoperability ensures that clinicians have access to complete, up-to-date patient information regardless of where data originates.
Healthcare system integration across these platforms improves care coordination, reduces duplication, and supports data-driven clinical workflows while maintaining secure data exchange.
Health Information Exchanges and Extended Networks
Healthcare organisations can share data via health information exchanges (HIEs) across agencies, regions, and the care network. When healthcare providers across agencies can access patients’ data regardless of which agency they are assigned to, it improves the ability to provide continuous care while still meeting regulatory and security guidelines.
To obtain interoperable data through HIEs, healthcare organizations must adopt standardized data formats, secure data transport mechanisms, and governance structures that support healthcare interoperability while complying with healthcare data security and regulatory requirements.
Device and Wearable Integrations
Data integration from medical devices and patient wearables is becoming a core capability of modern healthcare platforms, enabling continuous monitoring and remote clinical care. However, device interoperability introduces additional challenges related to data volume, variability, and security.
Healthcare software must support device and wearable integration using standardized interfaces and secure ingestion pipelines to ensure data accuracy, reliability, and compliance.
| Interoperability Component | Primary Purpose | Why It Matters in Healthcare Software Development |
|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
Typical Integration Challenges Healthcare Teams Face
Despite widespread adoption of interoperability standards, healthcare teams continue to face significant challenges when integrating systems across clinical, operational, and external environments. Integration barriers stemming from legacy systems and compliance requirements require healthcare software to be secure, scalable, and resilient.
Fragmented Legacy Systems
Healthcare organizations often operate a mix of contemporary platforms and legacy systems that were not designed for interoperability. These systems typically rely on proprietary data models or legacy messaging standards, thereby complicating and making healthcare system integration resource intensive.
Inconsistent Data Standards and Formats
Even with the adoption of standards such as FHIR and HL7, implementations still differ across vendors and healthcare environments. Variations in data representation, field use, and optional data can lead to misinterpretation of clinical data during system transfer. It requires effort from healthcare teams to normalize, validate, and govern data to ensure reliable data transfer between integrated systems.
Security and Compliance Constraints
Interoperability increases the number of access points through which healthcare data flows, expanding the potential attack surface. Healthcare teams must balance the need for seamless data exchange with strict healthcare data security and HIPAA compliance requirements. Balancing integration security with uninterrupted clinical workflows remains an ongoing challenge, particularly when third-party applications or external systems are involved.
Integration Performance and Reliability Issues
Healthcare information system integration solutions should support real-time or near-real-time data transfer without degrading system performance. System latency, message failures, and system downtime can directly impact healthcare processes and patient care. Reliable message delivery, retry mechanisms, and integrated health monitoring remain obstacles as the rate of new integrations increases.
Limited Visibility and Monitoring
Many integration failures go unnoticed until they affect downstream systems or clinical users. One factor leading to this is that we do not have a central point for monitoring integrations, lack sufficient logging, and have limited alerts, making it difficult for teams to find and fix problems quickly. Without adequate observability, organizations in the healthcare industry typically struggle to maintain trust in integrated systems and the accuracy of the data.
Vendor and Third-Party Dependencies
Healthcare system integration often involves multiple vendors, each with its own update cycles, APIs, and support models. Changes introduced by one vendor can break existing integrations, requiring rapid remediation. Coordinating across vendors while maintaining system stability and compliance places additional strain on healthcare IT teams.
Scaling Integration as Systems Grow
When healthcare organizations expand their services, implement new technology, or engage in a health information exchange, the need for integration increases exponentially. Architectures that rely on point-to-point integrations often become challenging to scale and maintain. Healthcare teams must redesign integration approaches to support long-term scalability without increasing complexity or operational risk.
Compliance Is Not a Checklist – It’s an Architecture Pattern
Compliance in modern healthcare software development is an architectural requirement, not a post-deployment exercise. Because regulatory requirements govern data storage, access, exchange, and protection, compliance must be addressed at the architectural level.
This is particularly important in the context of healthcare interoperability, where FHIR and HL7 integration, as well as API-based interactions, pose regulatory risks if compliance is not enforced. Secure development of healthcare applications ensures that regulatory policies are not compromised when data moves across platforms, partners, and healthcare networks.
Compliance-driven architecture typically includes:
- Embedded access control enforcement
- Built-in audit trails and logging
- Secure API and data exchange
- Standards-based interoperability controls
- Centralized policy and identity management
- Scalable governance for integrations
- Encryption at rest and in transit
- Continuous monitoring and anomaly detection
Real-World Use Cases
Modern healthcare software development must translate architectural principles such as security, interoperability, and compliance into real operational outcomes. The following real-world use cases illustrate how healthcare organizations apply healthcare interoperability, healthcare data security, and compliance-by-design to solve everyday clinical and operational challenges.
-
Integrated Electronic Health Records Across Care Settings: Enables secure sharing of patient data across EHR systems to improve care coordination and clinical decision-making.
-
Laboratory and Imaging System Integration: Delivers lab results and imaging data into clinical workflows securely and in near real time.
-
Health Information Exchange Participation: Supports regulated data sharing across organizations to ensure continuity of care beyond institutional boundaries.
-
Remote Patient Monitoring and Wearables: Supports regulated data sharing across organizations to ensure continuity of care beyond institutional boundaries.
-
Third-Party Clinical Applications: Allows secure integration of interoperable clinical apps within EHR environments while maintaining compliance and access control.
Recommended Healthcare Tech Stack
| Architecture Layer | Purpose |
|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
How a Healthcare Software Engineering Partner Helps
Today, the development of healthcare software requires much more than just functional applications. Security, interoperability, performance, and compliance have to be built into the system architecture to enable safe, connected, and scalable healthcare delivery. The healthcare industry can no longer afford a patchwork approach to security as the healthcare platforms continue to expand to include cloud computing, third-party applications, devices, and health information exchanges.
Implementing a strategic plan for security and interoperability will enable the healthcare industry to safeguard its data, comply with regulatory requirements, and ensure easy access to healthcare information.
Take the Next Step
Building secure, interoperable, and compliant healthcare platforms requires exemplary architecture, validation, and engineering expertise. Whether you’re modernizing legacy systems or designing new healthcare software, the next step is to assess gaps and act with confidence.
- Download the Healthcare Software Security Checklist to evaluate your platform against modern security, interoperability, performance, and compliance benchmarks.
- Read Healthcare Case Studies to see how complex healthcare systems are modernized securely and at scale.
- Book a Healthcare Architecture Consultation with Telliant Systems to get expert guidance on building resilient, HIPAA-compliant, and future-ready healthcare software.
Learn more at https://www.telliant.com
Technical debt has always been part of building software, but today it grows faster than most teams realize. With distributed architectures, endless integrations, and constant release pressure, complexity builds up quickly.
Even well-performing teams find that hidden issues and aging components creep in faster than they can manage. That is when legacy app modernization steps in as the most dependable way to stabilize systems and support business growth.
1. What Technical Debt Really Means Today
Old frameworks, temporary solutions, postponed migration work, and integrations that fail at scale are all sources of technical debt that were previously kept under control through gradual changes to legacy systems. Today, rapid CI/CD pipelines, cloud-native setups, and expanding microservices create far more chances for things to drift out of sync and introduce inconsistencies.
These factors typically show up as:
- Old frameworks that slow down development and modernization
- Temporary fixes that were never refactored
- Postponed migration work that accumulates over time
- Integrations that cannot be scaled with system growth
- CI/CD and cloud-native changes that introduce drift and inconsistencies
Legacy application modernization is now necessary for resetting the engineering foundation. It helps reduce long-term structural and code-level debt, through focused application modernization strategies that tackle both technology and architecture.
2. The Hidden Accelerators: Factors That Increase Technical Debt
Several modern-day factors have contributed to technical debt. These are frequently ignored until delivery intervals or performance start to decline.
-
Fragmented technology stacks
Teams use specialized tools across analytics, security, CI pipelines, communication, and deployment. Even though each tool addresses a different issue, maintaining the entire ecosystem becomes difficult. Updates, patches, and compatibility issues are increasing exponentially.
-
Pressure for constant releases
Product teams push for continuous delivery, but rapid cycles often introduce shortcuts. Temporary code becomes permanent far too often, accumulating across sprints and releases.
-
Cloud evolution and vendor dependency
Cloud providers regularly modify configurations, discontinue certain services, and update APIs. Teams that are unable to keep up are left with weaker security coverage, misaligned infrastructure, and version problems.
-
Skill gaps across engineering teams
Technologies such as serverless, orchestration, and distributed tracing evolve rapidly. When teams have different levels of expertise, it leads to inefficient implementations, duplicated services, and inconsistent architectural patterns.
-
Integration overload
Modern systems depend on external services for payments, authentication, analytics, and operations. Each integration brings additional maintenance needs and potential failure points.
-
Data growth beyond initial assumptions
Slow queries, storage concerns, and indexing challenges arise as data volume grows. A performance bottleneck is caused by what once worked.
3. How Modern Engineering Practices Can Backfire
Engineering teams adopt modern methods to increase scalability and improve delivery speed. Yet, without architectural governance, these practices can produce the opposite effect.
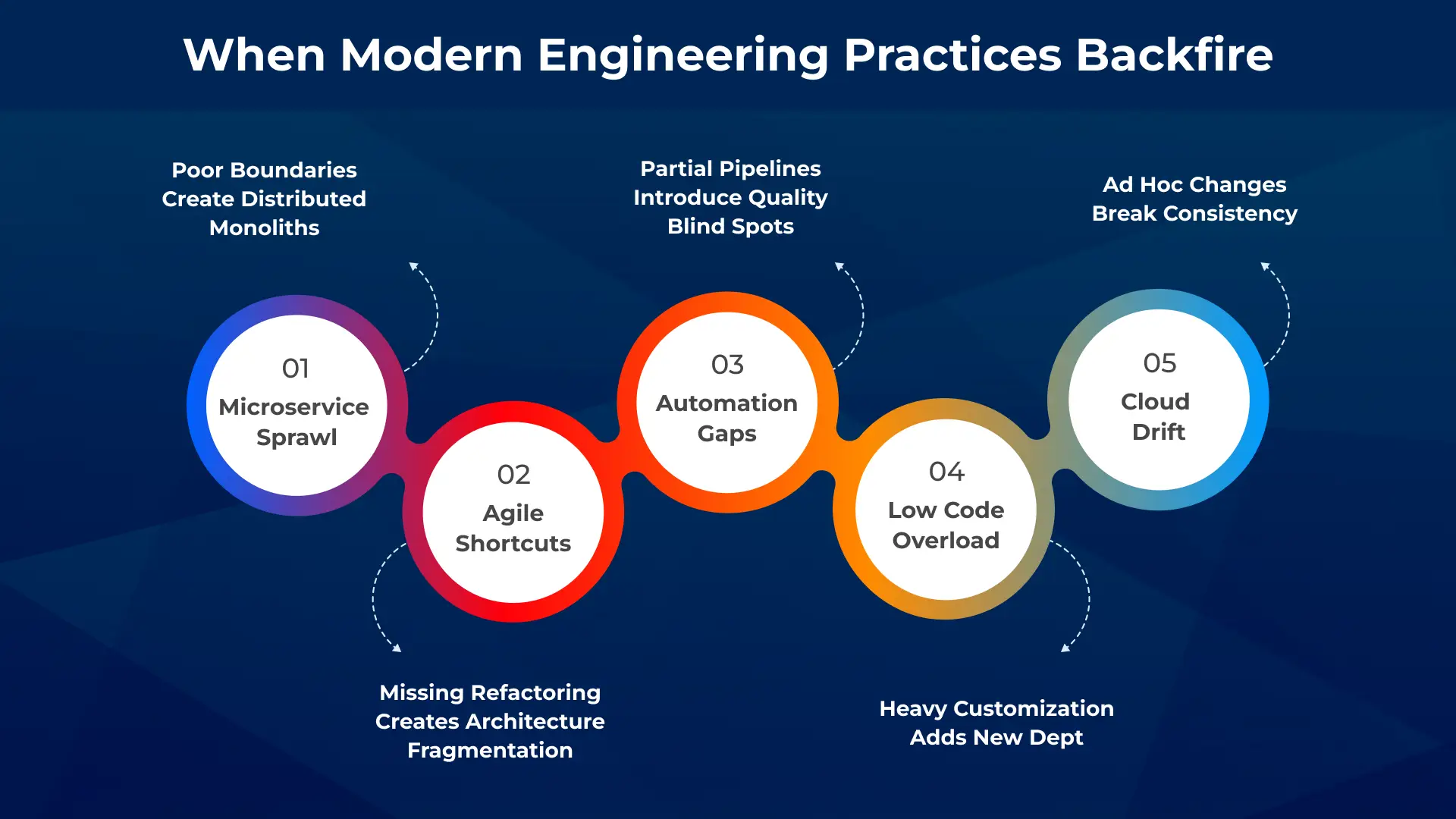
-
Undefined microservice boundaries
Microservices offer modularity, but when boundaries are unclear, they grow into tangled systems. This increases operational overhead and makes debugging, scaling, and testing far more complicated.
-
Agile without refactoring
Agile encourages quick delivery, but the architecture eventually breaks apart in the absence of specific cleanup cycles. While new features are still being released, technical debt quietly accumulates.
-
Partial DevOps automation
Although inconsistent test coverage leads to blind spots, automation improves reliability. While some components require little protection, others require extensive validation.
-
Over-customized low code
Low-code tools speed up development. Yet, heavy customizations create long-term maintenance challenges and add a new layer of technical debt.
-
Uncontrolled cloud drift
Infrastructure-as-code helps ensure consistency, but ad hoc environment changes cause drift. This leads to unpredictable behavior and harder-to-maintain cloud setups.
These examples show why many teams later turn to legacy app modernization or seek targeted application modernization strategies to restore architectural consistency.
4. The Real Cost: How Technical Debt Impacts Product Roadmaps and Performance
Each aspect of the product lifecycle is eventually impacted by technical debt. Teams spend more time managing problems and less time producing value due to outdated components, fragmented architecture, and increasing dependencies. As engineering’s focus shifts to maintenance, performance and scalability degrade, and release cycles slow down.
As security and compliance risks increase from unpatched parts of the system, the ability to innovate gradually decreases. It becomes challenging to execute product roadmaps predictably, and as a result, most companies are considering legacy application modernization to restore stability and enable long-term agility.
These impacts typically appear as:
- Slower feature delivery
- Performance and scalability issues
- Security and compliance exposure
- Reduced innovation capacity
5. Strategies to Identify, Manage, and Reduce Technical Debt
-
Conduct recurring codebase and architecture assessments
Every 2 or 3 months, perform audits to assess the architecture and codebase. Such a method helps spot the riskiest modules, outdated packages, and incorrect architectural patterns. With a structured scoring system in place, teams can prioritize which issues to address first and focus their fixes on the areas with the most significant impact.
-
Adopt a modernization roadmap
Legacy app modernization should be approached as a phased program covering architecture redesign, refactoring, API consolidation, cloud optimization, and database modernization. These phases serve as core application modernization strategies for long-term improvement.
-
Embed refactoring into sprint planning
Refactoring should not be an afterthought. Allocating a fixed percentage of each sprint for cleanup ensures continuous improvement.
-
Standardize engineering practices and architectural patterns
A strong engineering playbook with clear guidelines on frameworks, naming conventions, testing methods, and deployment strategies reduces inconsistencies across teams.
-
Prioritize modernization driven by business value
Not all debt is equally harmful. Businesses should upgrade the parts of their software that directly impact performance, scalability, compliance, or revenue. This disciplined approach reinforces legacy application modernization initiatives and ensures it delivers tangible results.
6. When to Ask for Help: Partnering With Engineering Experts
There is a time when the internal capabilities and skills are no longer sufficient to handle the increasing debt or to facilitate the modernization on a large scale. External engineering partners, like Telliant, help organizations accelerate modernization efforts, boost performance, and rebuild architectural foundations through structured legacy application modernization programs.
Organizations typically see substantial value in seeking support when they need
- A thorough approach to modernizing architecture
- Professional performance engineering for high-load systems
- Extensive codebase audits to find hidden dangers
- Capabilities for long-term product engineering for sustainable expansion
Expert partners bring methodologies, specialized skills, and the ability to execute complex application modernization strategies effectively.
Software-driven companies no longer compete only with features or speed to market. They now compete on how well they build, scale, and manage engineering operations across global talent networks, increasingly through a hybrid software development model. As digital platforms become more complex, delivery models that depend entirely on onshore or offshore teams find it harder to maintain speed, cost efficiency, and operational control simultaneously.
The hybrid software development model offers a distinct option by integrating onshore, nearshore, and offshore teams into a cohesive delivery framework. In this combined software development approach, onshore teams manage product strategy and design. Nearshore teams improve collaboration. Offshore teams handle extensive execution.
The sections that follow look at how teams engage, the technical basics, governance controls, and best practices that define effective hybrid delivery between offshore and onshore teams.
Engagement Models in Software Development
Enterprises generally operate within three primary engagement models. The onshore delivery option provides enterprises with real-time collaboration opportunities, closer alignment with regulations and laws, and seamless integration into their business; however, due to its premium nature, it costs more than other alternatives.
On the other hand, offshore delivery provides enterprises with significant cost savings and the ability to scale their businesses rapidly; however, with this model, enterprises often experience delays in team coordination, increased governance and security risks, and a lengthy timeframe for establishing data governance practices.
By merging onshore and offshore teams into a single integrated delivery system, the hybrid software development model strikes a balance between these conflicting factors. Businesses can optimize cost-effectiveness while preserving control, security, and the integrity of their architecture with a hybrid software development model.
This model is well-positioned to support cloud modernization, AI adoption, digital transformation, and the engineering of enterprise platforms.
Technical Considerations in Hybrid Engagement
Technology architecture and delivery frameworks are the factors that decide if a hybrid model will be a powerful source for growth or an operational inefficiency.
1. Frameworks for Collaboration and Delivery
Hybrid agile delivery ensures teams maintain regular sprint cycles, uniform backlog management, and coordinated release governance.
Onshore leadership is responsible for defining the roadmap, prioritizing the sprint, and validating the release. Offshore teams are mainly engaged in development and testing, which are done on a large scale.
2. Development and Integration Tools
Technology platforms serve as the control layer for cross-border execution. To enable efficient global team collaboration, a standard toolchain is necessary. Planning tools such as Jira, version control with GitHub or GitLab, CI/CD pipelines with Jenkins or Azure DevOps, and real-time communication via Slack or Microsoft Teams enable consistent, seamless coordination across distributed teams.
The key to successfully distributed DevOps is a robust, locally operated DevOps pipeline. An offshore developer should be able to carry out the same operations of development, testing, deployment, and monitoring in the environment as an onshore architect, without the need for any delays or manual handoffs.
3. Architecture Requirements
Legacy systems reduce the effectiveness of hybrid delivery because tightly coupled components and fragile dependencies limit flexibility and scalability.
To operate a hybrid-first environment, it is necessary to have modern, modular architecture with the following basic principles:
- A microservices-based, architecturally designed system to allow independent ownership of services
- API-first integration for maintaining a flawless connection with distributed systems
- Containerization through Docker and Kubernetes to be able to share the same environmental standard across different regions
4. Performance Considerations
In hybrid configurations, performance engineering often becomes a centralized offshore skill. These are continuous processes: automated scalability testing, cloud optimization, load testing, and system monitoring.
Platforms for unified observability make sure that application health is visible everywhere. This structure reduces performance risks in high-traffic production environments and enables proactive optimization rather than reactive firefighting.
5. Compliance & Security
The primary hurdle to trust in secure offshore development is security. Businesses need to incorporate security into both operational and architectural layers. This covers safe CI/CD pipelines, data encryption, multi-factor authentication, vulnerability scanning, and zero-trust access models.
Offshore compliance requirements such as ISO 27001, SOC 2, HIPAA, PCI-DSS, and GDPR should be incorporated into the contract and continuously audited.

Governance & Management Layer
Hybrid delivery can go beyond governance levels to serve as an integrated control framework rather than a reporting function. Efficient governance merges engineering execution, program management, business leadership, and compliance supervision into one operational structure.
Key governance components include:
- SLAs drive Performance Metrics.
- Risk Escalation Frameworks are established across regions.
- Integrated Quality Assurance.
- Security checkpoints are established between areas.
- Financial Transparency and Commercial Alignment across the World.
Best Practices for a Successful Hybrid Model
- Establish governance before scaling teams.
- Create the system architecture so that each module has its own owner.
- Standardize delivery processes globally.
- Automate security across the lifecycle.
- Consider the offshore teams as the partners in innovation.
- Use data-driven performance management.
Conclusion
The hybrid engagement model has become a foundational enterprise delivery strategy rather than a transitional outsourcing approach. When engineered correctly, the hybrid software development model delivers cost efficiency, global scalability, regulatory confidence, and sustained innovation velocity.
Hybrid engagement is not a compromise between offshore and onshore teams. It is a strategic operating model that unifies global talent into a single performance-driven delivery engine.
For organizations looking to implement or strengthen their hybrid strategy, Telliant helps enterprises adopt secure, scalable, and governance-led delivery across offshore and onshore teams.
A major financial services client recently shared a frustrating story with me. Their central data team had built a massive data lake consolidating information from over fifty different sources. The goal was simple: a single source of truth for the entire enterprise. Yet, their sales and marketing departments were still spending days each week preparing and reconciling data reports. The data was all there, in one place but it was slow, difficult to use, and the central team was a bottleneck for every new request.
This is a common challenge. You have invested in a centralized data repository, but the promised agility and insights remain just out of reach. This leads us to a major dilemma that you are confronted with today: will you stick to a centralized data lake, or will you look into the possibility of a decentralized data mesh? This is not purely a technical decision; it is a strategic one that will determine the extent to which your organization benefits from data in the coming years.
Let’s break down both software architectures in clear, practical terms.
What is a Data Lake? The Centralized Repository
A data lake is a centralized repository that allows you to store all your structured and unstructured data at any scale. You can keep data in its raw, native format without having to first structure it. This approach is built on the principle of schema-on-read flexibility, meaning the structure is applied only when the data is read for analysis, not when it is stored. This offers immense flexibility for exploration.
The tools that enable this are familiar and powerful. You might use AWS S3 or Azure Data Lake Storage as your primary storage. To process this data, you would use frameworks like Hadoop for distributed storage and Spark for large-scale data processing. The primary advantage is the simplicity of having one centralized repository. It provides a single source of truth for raw data at a low storage cost.
The data lake’s strength is its simplicity as a centralized repository. It gives you a single place to dump all your historical data for a low cost. But this is also its weakness. Without strict governance, the lake can quickly become a “data swamp” a disorganized pool where data is impossible to find or trust.
What is a Data Mesh? The Decentralized Domain-Based Model
The data mesh proposes a different answer. Instead of one central lake, data mesh is a decentralized, domain-oriented architecture where data ownership is distributed to the business domains that create and use the data most closely. Sales owns the sales data, finance owns the finance data, and the DevOps team owns the operational data.
In a data mesh, each domain team treats its data as a product. They are responsible for providing standardized productized data sets that are discoverable, secure, and interoperable. This shift drives improved domain alignment because the people who understand the data best are the ones managing it.
This approach drives scalability through decentralization. As your organization grows and new domains emerge, they can onboard themselves without overburdening a central team. This model relies heavily on a foundation of decentralized data governance, where global standards are set, but domains have the autonomy to implement them.
Key Differences: Centralized Control vs. Decentralized Ownership
| Topic | Data Lake | Data Mesh |
|---|---|---|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
|
According to a report by the U.S. Government Accountability Office, the challenges of managing fragmented and siloed data across agencies highlight the immense difficulty of centralized control at scale. This underscores the problem that data mesh aims to solve.
When Should You Choose a Data Lake?
The data lake is not obsolete. It remains a powerful and correct choice for specific scenarios.
Choose a data lake if:
- Your primary need is a low-cost landing zone for massive volumes of raw, historical data, such as application logs or IoT sensor data.
- Your data science team is small and focused on exploratory, ad-hoc analysis where schema-on-read flexibility is a requirement.
- You have already made significant investments in a cloud data platform like AWS or Azure and want to leverage those credits for storage and processing.
- Your organization is not yet prepared for the cultural shift toward decentralized ownership.
The data lake excels as a central archive and a discovery sandbox. But you must ask yourself: are you prepared to implement the rigorous governance needed to prevent it from becoming a swamp?
When Should You Choose a Data Mesh?
The data mesh is a strategic response to organizational complexity and scale.
Choose a data mesh if:
- You have many independent teams (e.g., sales, finance, DevOps) that both create and need to share data.
- Your central data team has become a bottleneck, unable to keep up with requests from the business.
- Data quality is inconsistent because the central team lacks the specific business context to properly curate the data.
- Your enterprise analytics strategy is being slowed down by data delivery times.
Adopting a data mesh is a significant operational shift. It requires investing in training for your domain teams and leadership that supports decentralized data governance. The reward is an organization that can scale its data capabilities efficiently and reliably.
Can a Data Mesh and a Data Lake Coexist?
You do not necessarily have to make a binary choice. Many successful organizations adopt hybrid approaches.
In a hybrid model, the data lake continues to serve as the raw data landing zone. It is the “source of sources.” From there, domain teams are empowered to pull their relevant data, apply quality checks and business logic, and then publish it as a curated data product for the rest of the organization to consume.
For example, you could use AWS S3 as your central lake. The marketing domain then pulls raw clickstream data from the lake, cleans it, enriches it with customer information, and publishes a “Customer Journey” data product to a central catalog. This approach preserves the schema-on-read flexibility of the lake for exploration while providing the reliability of standardized productized data sets for production use. A thoughtful hybrid strategy often requires careful planning, an area where the data engineering experts at Telliant Systems can be invaluable in bridging architectural paradigms.
Technical Considerations Before You Decide
Your final decision must be grounded in your organization’s reality.
-
Team Skills
Do you have a strong central team of data engineering specialists, or do you have domain experts with the willingness to learn data management principles?
-
Budget
Data lakes can start cheaply, but Data meshes require upfront investment in data product platforms, catalogs, and API gateways to enable decentralized data governance.
-
Tools
Are you prepared to manage a landscape of Spark jobs in a lake, or a federation of domain-owned data products with their own pipelines?
-
Security
A lake offers one central vault to secure. A mesh requires a federated security model where domains control access to their products within a global policy framework.
The goal is to turn data from a challenge into your most powerful asset. The data lake offers a straightforward path for consolidation. The data mesh offers a scalable path for empowerment. The right architecture is the one that matches your people, processes, and ambition.
You do not need to make a final, all-or-nothing decision today. Start with a prototype. Ingest a new dataset into an AWS S3 bucket and see what it takes to make it useful. Or identify one willing domain team and help them build and publish their first data product. The journey to a smarter modern data architecture begins with a single, deliberate step.
If you are evaluating how to structure your data infrastructure for scale, our team at Telliant Systems has deep expertise in guiding companies through these critical decisions. Explore our software product development services to see how we can help, or learn more about our specific approaches to data engineering and DevOps to ensure your data architecture is built for performance and growth.
Cloud computing has refined how many enterprises deploy, scale, and maintain their software. But as the convenience slowly grows, the cost rises, on the other hand. In initial phases of adoption, cloud spend is seen as an acceptable byproduct of agility. With time, however, the time we spend quietly balloons, hidden behind resource sprawl, overlapping subscriptions, and untraced data transfers.
As per the latest 2025 report conducted by Flexra State of the Cloud, 84% of respondents believe that managing cloud spend is the top cloud challenge for organizations today. Many organizations are identifying that scaling cloud infrastructure without strong financial governance can distort margins faster than it drives innovation.
Cloud optimization isn’t just an engineering concern; it’s a complete C-suite priority. The real objective is how it aligns with the Cloud App Development efforts with measurable business outcomes, making sure that every dollar spent directly helps support growth, performance, and innovation.
Technical Cost Optimization Practices
The basic foundation of optimization is to understand the utilization. Once the team gains strong visibility into idle or oversized resources, they can strategically apply the right measures to the right-size infrastructure and could potentially reduce a lot of waste.
-
Right-Sizing and Auto-Scaling
AWS Compute Optimizer, Azure Advisor, and GCP Recommender provide cost and performance recommendations that are based on usage trends. Adopting AWS Auto Scaling Groups or Azure Virtual Machine Scale Sets enables workloads to adjust them to demand, a simple but impactful cost lever. Many businesses have reported seeing a major 20-40% savings on total spending right after implementing right-sizing policies in production environments.
-
Leveraging Reserved and Spot Instances
AWS Savings Plans, Azure Reserved Instances, and GCP offer certain discounts to cut costs significantly for predictable workloads. For temporary or fault-tolerant jobs, Spot Instances or Preemptible VMs can reduce compute expense over time, which in the long run is ideal for the large-scale analytics or machine learning training pipelines.
-
Storage and Data Lifecycle Management
Storage becomes one of the hidden costs that sinks. Solutions such as Amazon S3 Intelligent-Tiering, Azure Blob Storage tiers, and GCP Coldline Storage automatically move less-frequent data to cheaper layers. Combined with data retention policies, it helps the team avoid paying for data that no one ever uses.
-
Serverless and Container Optimization
An additional frequently missed option for tuning performance in the cloud is leveraging serverless architectures. AWS Lambda, Azure Functions, and Google Cloud Run are examples of services that allow you to only pay for execution time instead of having to provision servers that sit idle. Also, optimizing workloads that use containers with properly sized Kubernetes clusters and autoscaling of node pools continues to improve resource utilization while keeping performance in check.
-
Cloud Operations Best Practices
Incorporating Cloud Operations with the best practices, such as automated cost notifications, usage tagging, and policy-based shutdowns, ensures that there’s continuous governance. When acted on correctly, these operational standards can actually transform cloud efficiency from a reactive task into a proactive discipline.
Monitoring & Tooling
Optimizing without proper monitoring is like driving without a dashboard. AWS Cost Explorer, Azure Cost Management + Billing, and GCP Cloud Billing Reports remain the core visibility tools for most enterprises. Regardless, multi-cloud environments need consolidated intelligence, platforms such as CloudHealth by VMware, Spot.io, or FinOut, unify usage data, and assess a complete picture of cost, consumption, and ROI across providers. Building a culture of FinOps is equally important. FinOps (Financial Operations) is not a tool but rather a collective mindset – a combination of finance, engineering, and product management. With FinOps, spending decisions are more transparent, and CTOs and CFOs can work together using live data instead of relying on quarterly reports.
Multi-Cloud vs Single Cloud
Deciding between single-cloud and multi-cloud architecture defines the flexibility and your financial complexity.
Single Cloud:
- Simplifies governance and standardizes tooling.
- Offers deeper service integration (e.g., AWS Lambda + DynamoDB or Azure Synapse + Power BI).
- Easier to secure and monitor at scale.
Multi-Cloud:
- Prevents vendor lock-in and allows selective adoption of best-in-class services.
- Enhances resilience through workload distribution across providers.
- Demands strong multi-cloud optimization strategies, unified identity management, and cost aggregation tools to maintain visibility.
For most entrepreneurs, a hybrid model that uses one core cloud for the Cloud app development and others for special use cases, offers an optimal balance between agility and control.
Case Example: Real Optimization in Action
A SaaS analytics company operating across AWS and GCP once struggled with ungoverned resource usage. Their estimated bill was $420,000 due to underutilised EC2 clusters and duplicated datasets.
Right after implementing auto-scaling, reserved instance commitments, and S3 lifecycle management, the organisation got to know that:
- 35% compute cost reduction
- 22% storage cost savings
- 18% performance improvement through active cloud performance tuning.
Above cost, these actions improved reliability and time-to-market, driving some of the measurable cloud migration ROI that resonates with technical and financial stakeholders.
Checklist for CTOs: Sustaining Cloud Cost Optimization
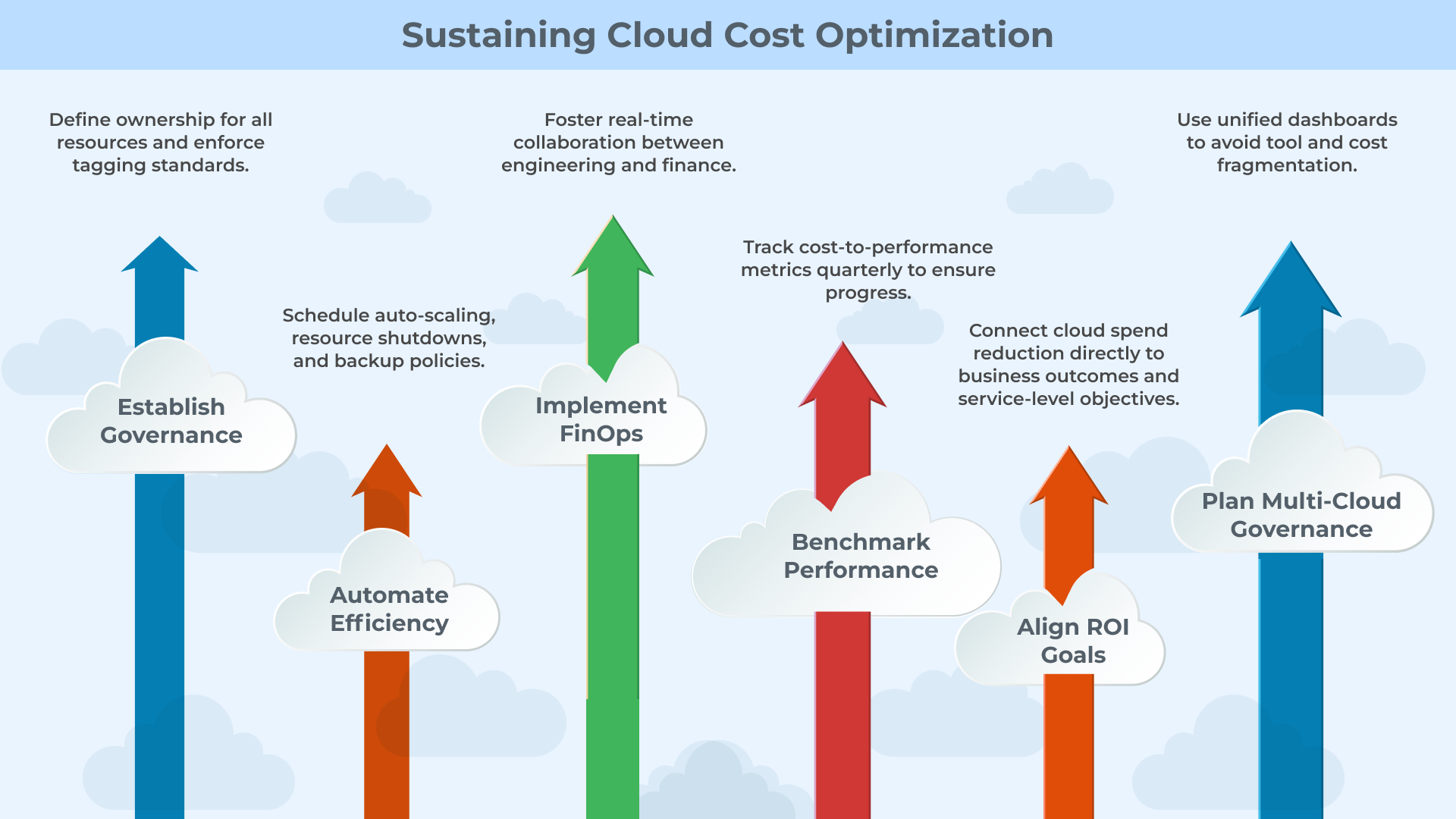
-
Establish Governance
Define ownership for all resources and enforce tagging standards.
-
Automate Efficiency
Schedule auto-scaling, resource shutdowns, and backup policies.
-
Implement FinOps
Foster real-time collaboration between engineering and finance.
-
Benchmark Performance
Use unified dashboards to avoid tool and cost fragmentation.
-
Align ROI Goals
Connect cloud spend reduction directly to business outcomes and service-level objectives.
Conclusion
Sustainable cloud transformation is a matter of precision, not scale; in fact, as organizations evolve in their digital ecosystems, cloud cost optimization becomes a foundational element of operational resilience, allowing organizations to support true innovation without diminishing their efficiency. We at Telliant Systems leverage Cloud Operations best practices throughout the Cloud App Development process. We start utilizing these best practices during architectural design and retain them during performance monitoring.
We utilize automation, governance, and multi-cloud optimization, while enabling teams to understand ROI from cloud migrations as an organization, all while retaining performance, security, and scalability built into their systems. In today’s world, the true measure of cloud maturity is innovation that is cost-effective, and performance based.





































